Diplomacy and Intelligence

by James Lee
This note comes in the wake of the revelations that that had been a cyber attack on Singapore. 1.5 millions Singaporeans were affected. According to news articles, this was a deliberate attack, suggesting some sort of state influence in it. Naturally, many Singaporeans were outraged. Responses varied from questioning why it took so long for the news to be made known, questioning the competency of the people in charge (read: paper generals etc), questioning why the public was not given full information as to who the culprits were, whose head would roll etc.
First of all, I would like to caution all Singaporeans who are on the verge of embarking on a witch hunt to hold your horses and let us be level headed here. As citizens, we can demand accountability, yes. But do not demand it for the sake of demanding it. Singaporeans are known for being complainers, but let us take it one notch down instead of baying for blood. Also, for those who do not belong to the cybersecurity or the intelligence community, please refrain from being armchair critics - cyber security and intelligence is not a game, especially not now.
Information
This is the key gripe that we all have. Georgia Tong asserts that too much information has been withheld from the public. For those not in the know, this was intentional and deliberate. Let me re-emphasize: Intentional and deliberate. The rational behind releasing only pertinent and sufficient information is to prevent a panic. Let us, for argument sake, examine a hypothetical scenario:
Suppose Minister Gan and Iswaran comes out and says this: “Our investigations have revealed that China was behind the cyber attack”. One can only imagine what will happen next. There will be racial backlash against the mainland Chinese in Singapore, boycotts on Mala Xiang Guo and Hai Di Lao, Chinese ‘service providers’ in Geylang, etc. In China, 2 billion people will start to flame Singapore and Singaporeans on Weibo, our China branches of BreadTalk, Ya Kun will be subjected to Chinese fury and suddenly we are China’s no.1 enemy. If this sounds familiar, it is the rhetoric and the theatrics that Trump is employing and truth be told, it is backfiring on all aspects.
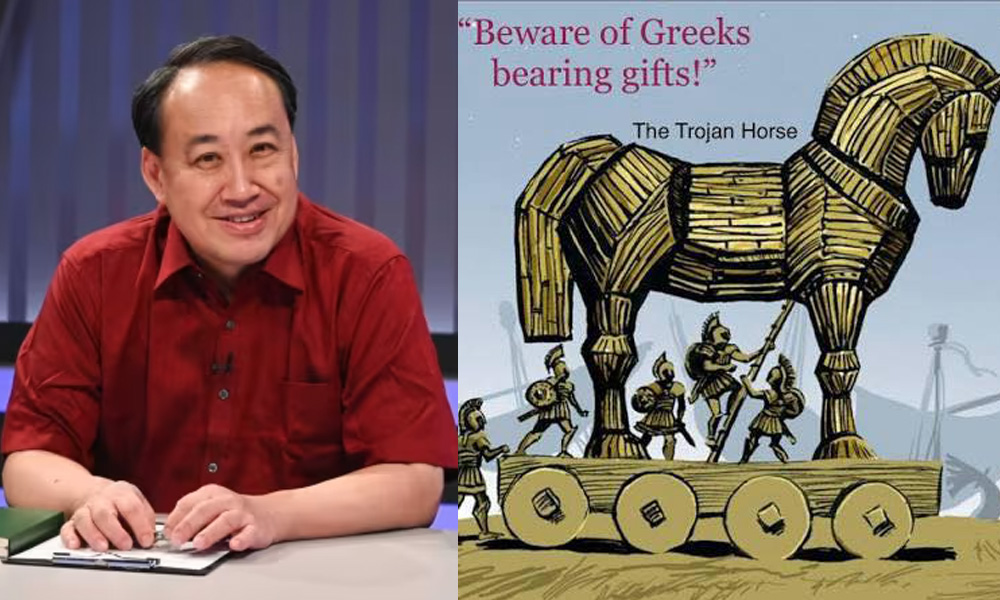
The value of information withheld has its advantages. Zhuge Liang’s success at Red Cliff was not as a result of him announcing to Cao Cao or the public that he was waiting for the Easterly wind at Red Cliff. The information was withheld and only made known when it was too late for the enemy and when it was overwhelmingly advantageous to him. Furthermore, there was no value in announcing that China or Russia was behind the attacks. Would Singapore be so gutsy as to declare war on them? Given our status as a small but neutral nation, I highly doubt so. Just a side note that if we really do so, I would so love to have all the keyboard warriors who are baying for blood now don their No.4 and report to the nearest camp to draw arms. However, since that is not happening, let us all calm ourselves down and stop saying things that are potentially embarrassing. The truth is, we are not going to war, hence no point in identifying who the enemy is. It is much better to withhold that information for now, and use that to our advantage later.
There were some who were also questioning why our ministers downplayed the consequences of the attack, choosing to call it a ‘serious breach’ rather than condemning it as ‘an act of war’:
Again, this is probably deliberate. The announcement on the attack would probably be watched by the hackers, hoping to capitalise on our response. Why was it not called an ‘act of war’ was explained in the previous paragraph; we are not going to declare war. Period. That is not the mission of the SAF. By intentionally downplaying the attack, it sends a signal to the attackers that they probably did not do as much damage as they thought they did. By coming out to say this first, it then forces the attackers to prove otherwise, and if they do so, they would have revealed their identity and earned the condemnation of others in the international community. Zitseng was concerned with the identity theft of all his personal particulars, and rightly so. The identity and NRIC numbers of individuals are important. However, what is to stop the government from issuing new NRIC numbers to those affected? I would not be surprised if the government really does this since there are advantages to doing so. First, it would invalidate the usefulness of the data the hackers obtained. Second, it reinforces the point that the data the hackers obtained was insignificant anyway.
Competency
I read with disappointment that there were those who questioned the competency of BG David Koh, who was supposedly parachuted into the top role at the CSA. https://www.theonlinecitizen.com/2018/07/23/singhealth-cyberattack-another-military-general-another-epic-failure/ This, to me, is plain wrong. It is right to question the competency of Desmond Kuek, who was parachuted into an engineering company, or the competency of Ng Yat Chung, who was parachuted into SPH. I agree that these two men, as qualified as they claim, are not the most technically competent for their role. However, BG Koh graduated from King's College London with a bachelor's degree in electrical and electronics engineering and a Master's in public administration from Harvard University. His previous roles include: Chief Signal Officer and Head of Joint Communications and Information Systems Department in the Joint Staff. If his CV and his military background does not make him the most qualified man to lead the agency for cyber security, I don’t know who else would be. Steven Lim perhaps? Again, let us refrain from complaining for the sake of complaining.
Smart Nation
In the light of recent events, some have questioned if we should be ‘Smart’ instead of ‘Secure’. It is a valid question, but Ghui is right to ponder that. However, from an intelligence and a strategy perspective, moving forward with Smart Nation is the correct approach. This is a deliberate and strategic move. It signals the hackers that their minor success in the SingHealth case has not derailed our plans. It belittles and undermines them. If we do a U-turn and start panicking about our security infrastructure, the hackers would know that they have hit us where it hurts and they will continue their assault. It is the same message that every government that had been the subject of terrorist attacks tells their citizens: Be stronger, carry on your lives as normal and do not let terror define your lives. It is the same for us.
In conclusion, and if I may draw an analogy, this whole situation is like a boxing match. We are up against a mightier boxer. In the hacking attacks, he has thrown a punch that lands below the belt. The referee and the crowds are eyeballing him now, jeering him for underhand tactics. We have dodged that punch a little and although it hurts, we do not show it. Showing pain is letting the opponent know that we are injured. Instead, we brush it aside casually, and signal to him not to try that again. If the opponent carries on playing dirty, we let the referee disqualify him. If not, we continue the delicate dance around the ring. Such is diplomacy, and such is intelligence. If I may also add, our government is highly proficient in both. As citizens, it is our duty to seek accountability for such lapses, but let us all do so with objectivity and not start a witch hunt.