Tech
StarHub: Two breakdown due to malicious DDOS attacks on its servers

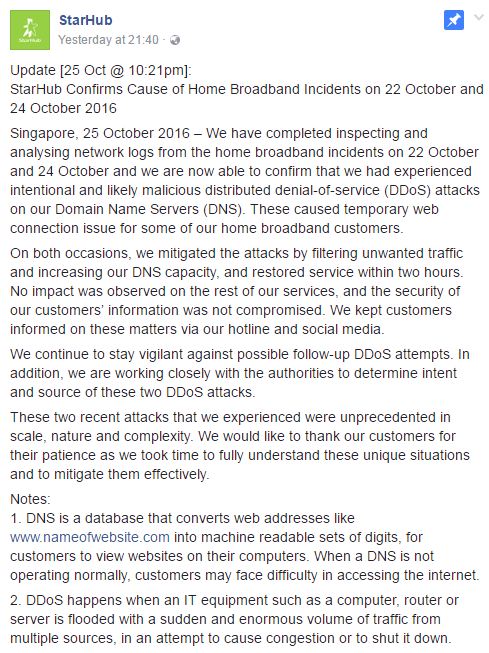
StarHub had said on Tuesday (25 October) that according to the inspection and analysis of network logs from the home broadband incidents on 22 and 24 October, it had experienced intentional and likely malicious distributed denial-of-service (DDoS) attacks on its Domain Name Servers (DNS).
DNS is a database that converts web addresses like www.nameofwebsite.com into machine readable sets of digits, for customers to view websites on their computers. When a DNS is not operating normally, customers may face difficulty in accessing the internet.
Starhub said that it had detected a spike in data traffic coming into its Domain Name Servers (DNS) on 24 October 2016 at about 10pm, temporarily affecting the web connection for some of its home broadband customers.
it immediately started filtering the unwanted traffic and added DNS capacity to manage the sudden and huge increase in traffic load. As a result, some customers temporarily faced intermittent broadband access.
However, its home broadband service for affected customers was fully restored at about 11:25 pm the same day.
It also said that there was no impact on mobile, enterprise and home voice services, and the security of its customers’ information was not compromised.
StarHub said that it mitigated the attacks by filtering unwanted traffic and increasing our DNS capacity on both occasions and restored service within two hours.
“No impact was observed on the rest of our services, and the security of our customers’ information was not compromised. We kept customers informed on these matters via our hotline and social media,” it wrote.
StarHub said that it continue to stay vigilant against possible follow-up DDoS attempts, therefore, it is working closely with the authorities to determine intent and source of these two DDoS attacks.
DDoS happens when an IT equipment such as a computer, router or server is flooded with a sudden and enormous volume of traffic from multiple sources, in an attempt to cause congestion or to shut it down.