Current Affairs
New phishing attack almost impossible to detect on Chrome, Firefox and Opera

A Chinese infosec researcher, Xudong Zheng, has discovered a new phishing attack that is ‘almost impossible to detect’, which could deceive even the most careful users on the Internet.
He wrote on his blog that Punycode makes it possible to register domains with foreign characters. It works by converting individual domain label to an alternative format using only ASCII characters. For example, the domain “xn--s7y.co” is equivalent to “短.co”.
From a security perspective, Unicode domains can be problematic because many Unicode characters are difficult to distinguish from common ASCII characters. It is possible to register domains such as “xn--pple-43d.com”, which is equivalent to “аpple.com”. It may not be obvious at first glance, but “аpple.com” uses the Cyrillic “а” (U+0430) rather than the ASCII “a” (U+0041). This is known as a homograph attack.
Fortunately modern browsers have mechanisms in place to limit IDN homograph attacks. The page IDN in Google Chrome highlights the conditions under which an IDN is displayed in its native Unicode form. In Chrome and Firefox, the Unicode form will be hidden if a domain label contains characters from multiple different languages. The “аpple.com” domain as described above will appear in its Punycode form as “xn--pple-43d.com” to limit confusion with the real “apple.com”.
Chrome’s (and Firefox’s) homograph protection mechanism unfortunately fails if every characters is replaced with a similar character from a single foreign language. The domain “аррӏе.com”, registered as “xn--80ak6aa92e.com”, bypasses the filter by only using Cyrillic characters.
“You can check this out yourself in the proof-of-concept using Chrome or Firefox. In many instances, the font in Chrome and Firefox makes the two domains visually indistinguishable,” Zheng wrote.
It becomes impossible to identify the site as fraudulent without carefully inspecting the site’s URL or SSL certificate. This program nicely demonstrates the difference between the two sets of characters. Internet Explorer and Safari are fortunately not vulnerable.
Chrome
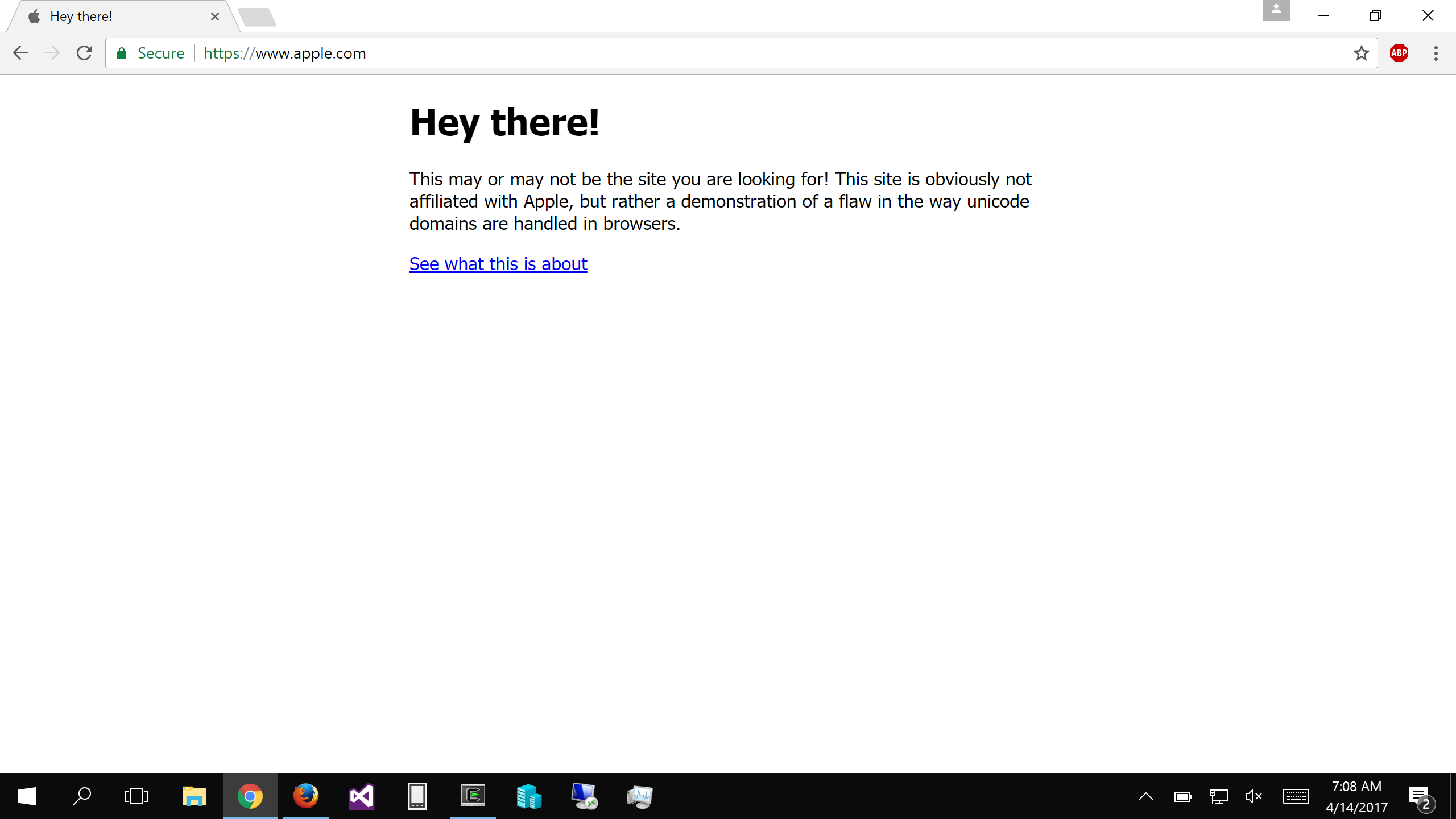
Chrome / source: xudongz.com
Firefox
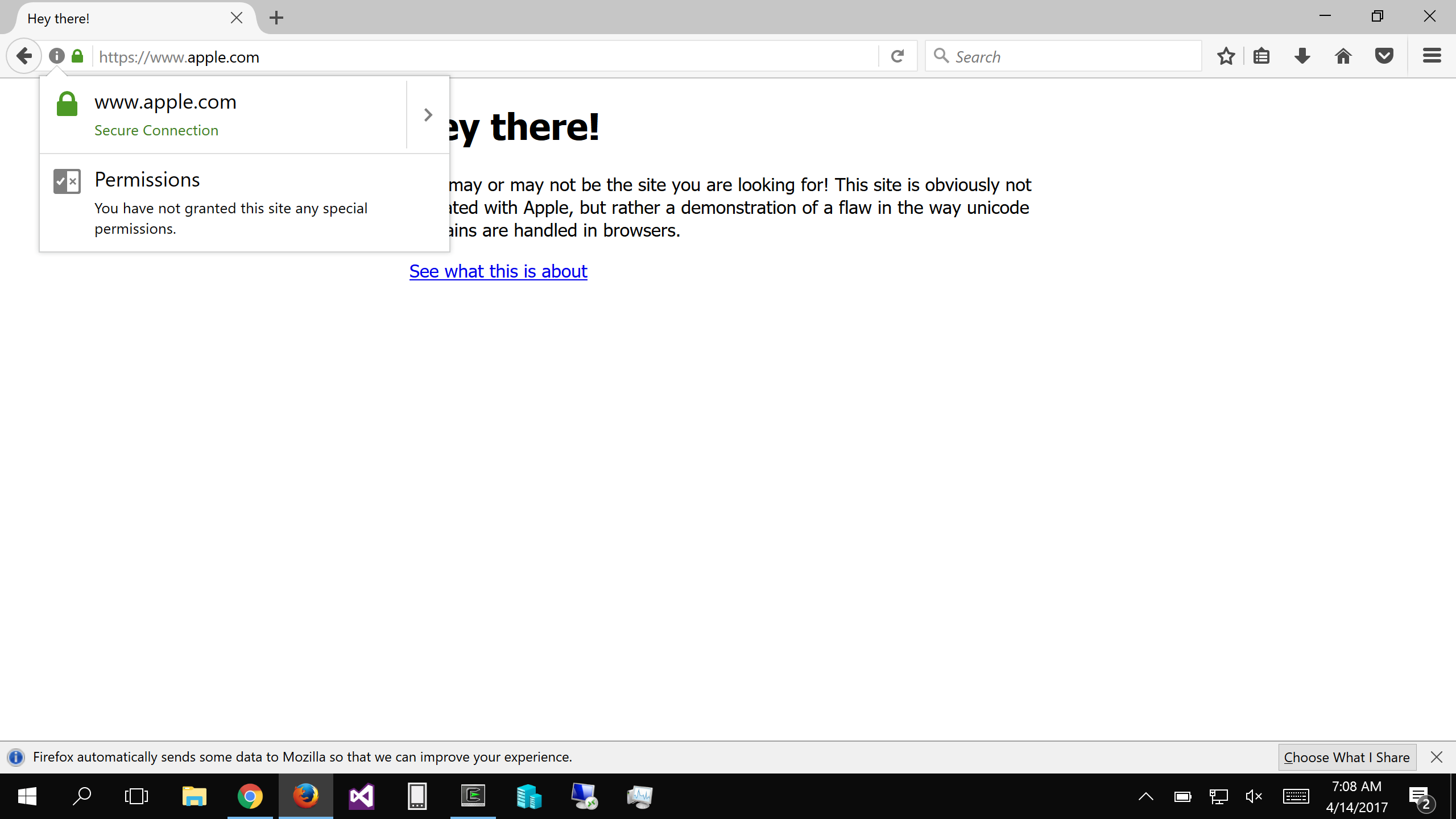
Firefox / source: xudongz.com
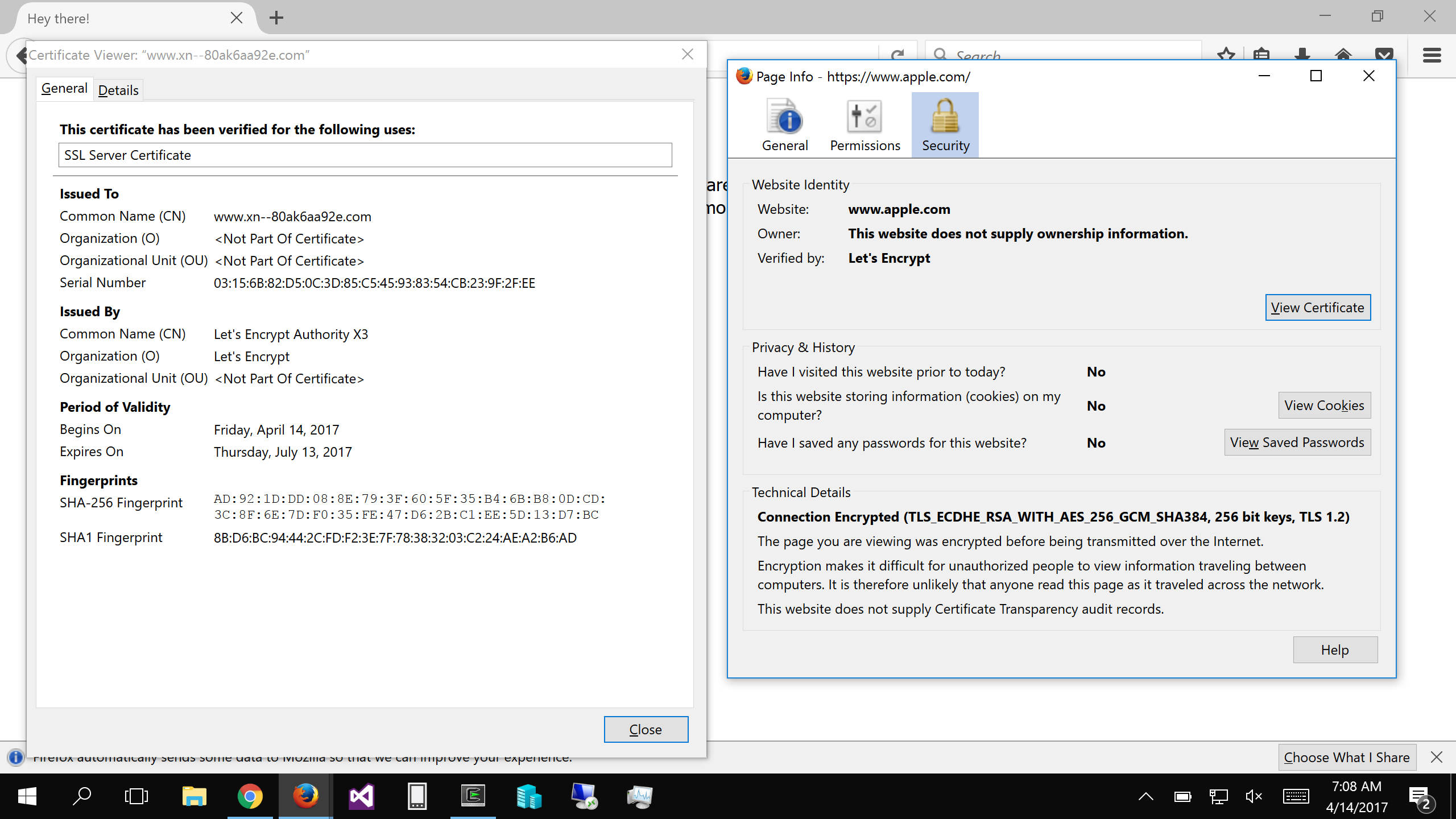
Firefox SSL / source: xudongz.com
However, Firefox users can limit their exposure to this bug by going to about:config and setting network.IDN_show_punycode to true. This will force Firefox to always display IDN domains in its Punycode form, making it possible to identify malicious domains.
“Thanks to /u/MARKZILLA on reddit for this solution,” Zheng acknowleged.
Firefox users can follow below-mentioned steps to manually apply temporarily mitigation:
Type about:config in address bar and press enter.
Type Punycode in the search bar.
Browser settings will show parameter titled: network.IDN_show_punycode, double-click or right-click and select Toggle to change the value from false to true.
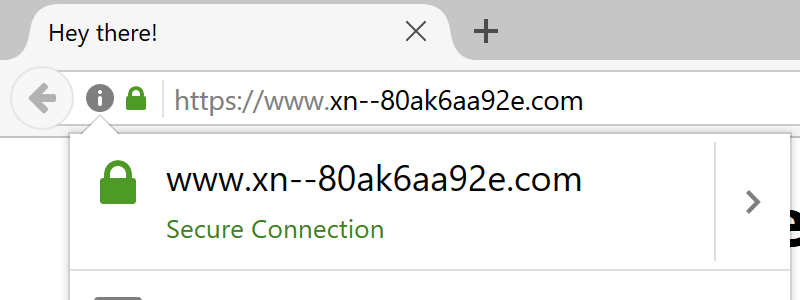
image source: xudongz.com
Opera
Unfortunately, there is no similar setting available in Opera to disable Punycode URL conversions manually, Zheng said.
He adviced, a simple way to limit the damage from bugs such as this is to always use a password manager. In general, users must be very careful and pay attention to the URL when entering personal information.
You can also follow Zheng on Twitter @Xudong_Zheng









